by CPI Staff | May 9, 2026 | Blog, Endpoint Management, Endpoint Security, Entra ID, Microsoft Intune
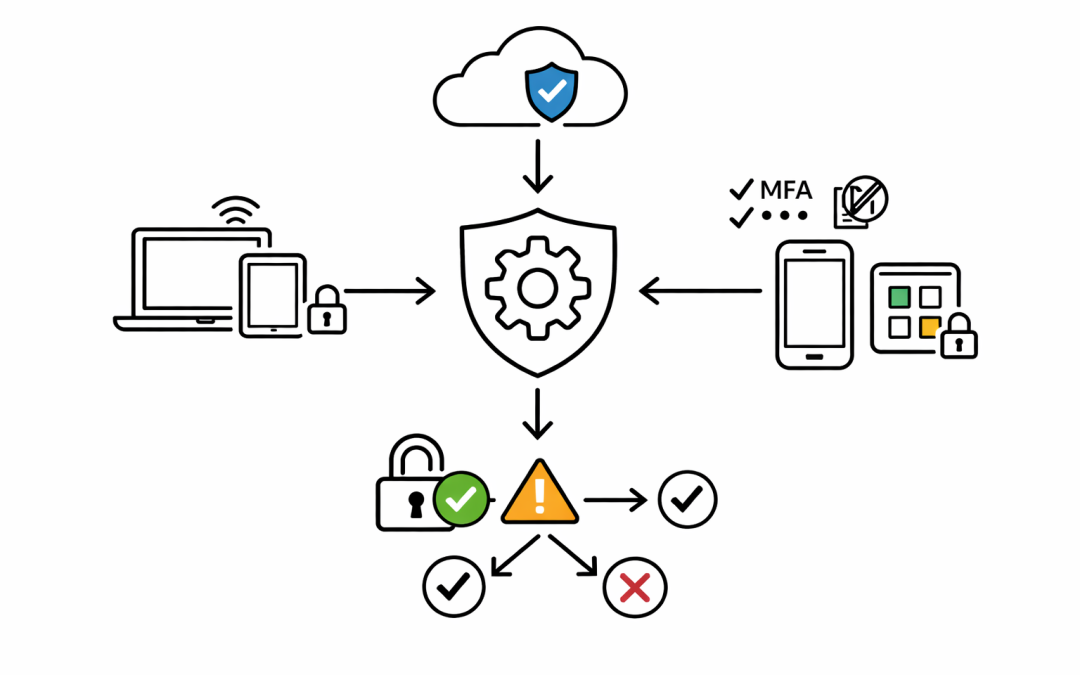
Too many Microsoft 365 security projects stall at the same point. Multi-factor authentication is on, devices are enrolled, and policies exist in a few different admin portals, but leadership still cannot answer a simple question: can an unmanaged or unhealthy device...

by CPI Staff | May 5, 2026 | Blog, Endpoint Management, Microsoft Intune
Most businesses already know device sprawl is a problem. Laptops leave the office, personal phones access company email, new starters wait too long for setup, and IT teams end up choosing between control and convenience. That trade-off is usually a sign that device...

by CPI Staff | May 1, 2026 | Blog, Cloud Security, Cybersecurity, Entra ID, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Intune, Microsoft Purview
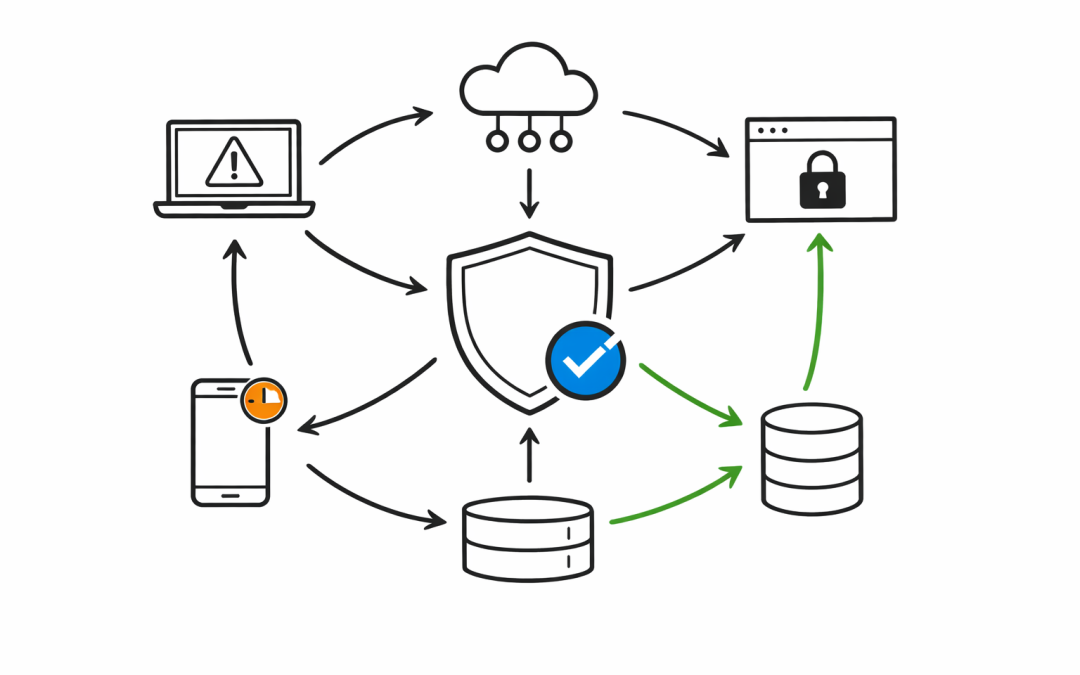
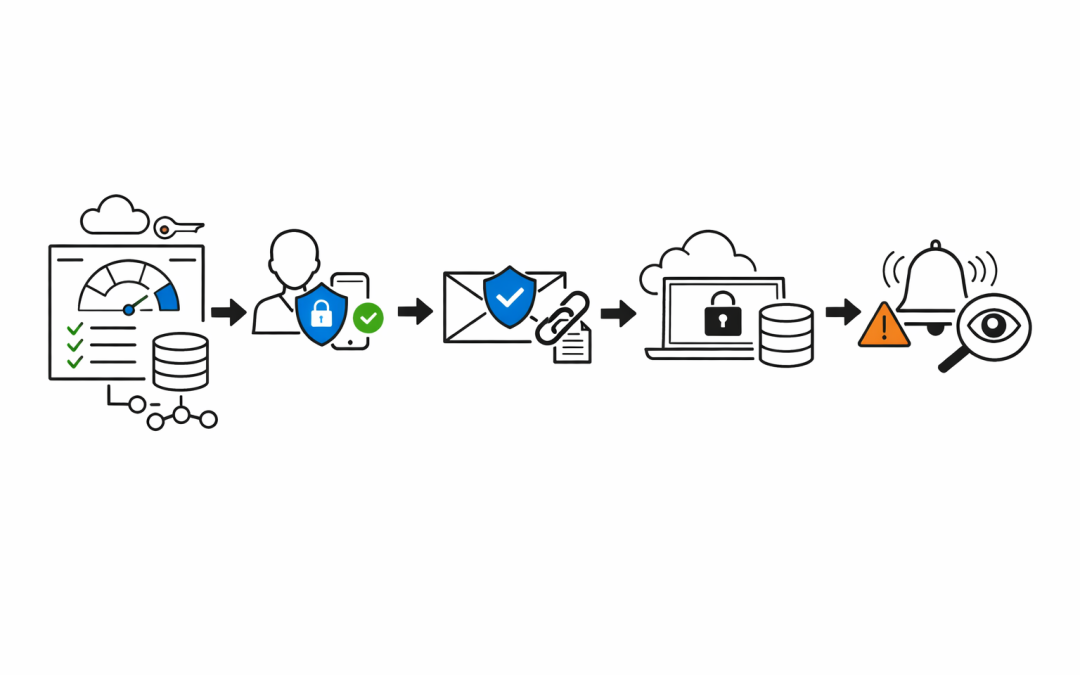
When a business enables Multi-Factor Authentication and calls it “done,” they’ve taken one important step — but left the door wide open in a dozen other places. MFA blocks a significant portion of credential-based attacks. Microsoft’s own data...

by CPI Staff | Apr 30, 2026 | Blog, Cybersecurity, Endpoint Security, Microsoft Intune
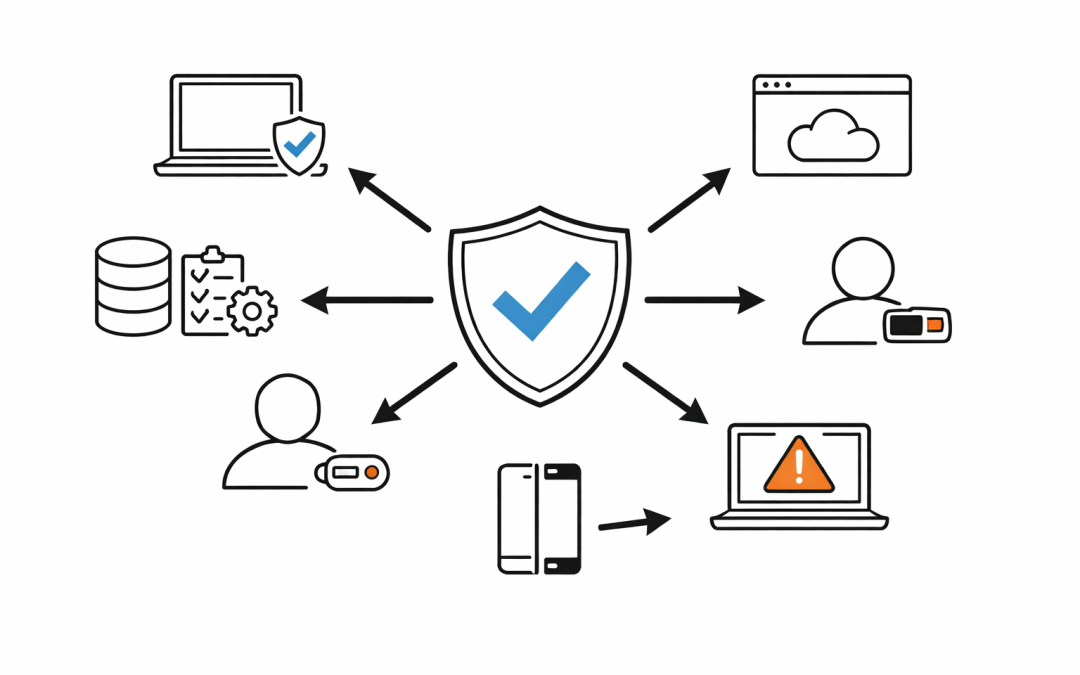
Most organisations assume that once their devices are enrolled in Microsoft Intune, those devices are secure. That assumption is wrong — and it’s costing them. There is a default configuration in Intune that silently marks every device without a compliance...

by CPI Staff | Apr 30, 2026 | Blog, Cloud Security, Cyber Security Strategy & Governance, Cybersecurity, Entra ID, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Intune, Microsoft Purview
Small businesses are not small targets. Threat actors know that organisations with fewer than 50 staff rarely have a dedicated security team. They know Microsoft 365 is the backbone of most Australian SMBs — email, files, Teams, identity. And they know most of those...

by CPI Staff | Apr 30, 2026 | Blog, Cybersecurity, Microsoft 365, Microsoft 365 Security, Microsoft Intune
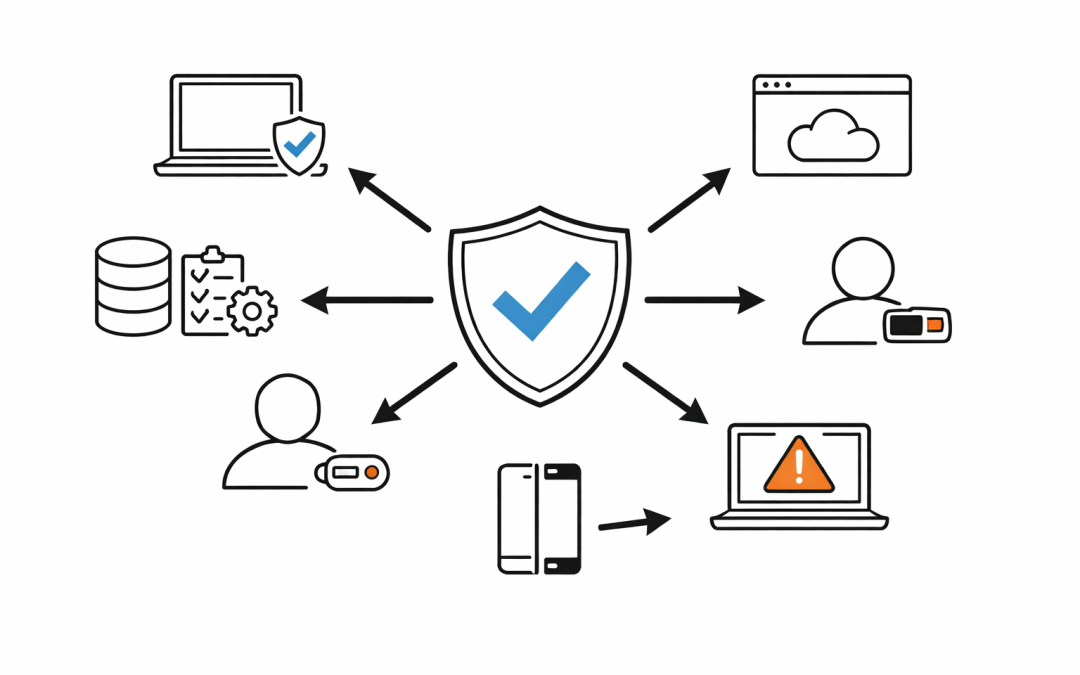
Most Australian organisations have invested in Microsoft 365 licences, security policies, and compliance controls. But there is a gap that regularly gets overlooked — and attackers know exactly where it is. Unmanaged devices. A personal laptop, a contractor’s...