by CPI Staff | May 1, 2026 | Blog, Cloud Security, Cybersecurity, Entra ID, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Intune, Microsoft Purview
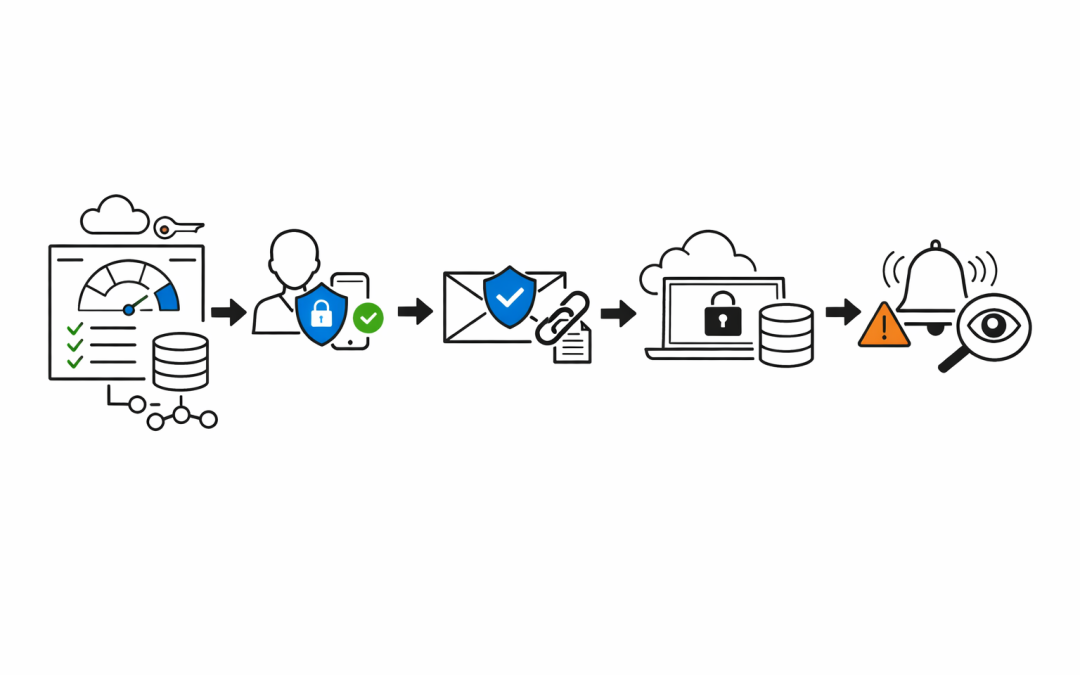
When a business enables Multi-Factor Authentication and calls it “done,” they’ve taken one important step — but left the door wide open in a dozen other places. MFA blocks a significant portion of credential-based attacks. Microsoft’s own data...

by CPI Staff | Apr 30, 2026 | Blog, Cloud Security, Cyber Security Strategy & Governance, Cybersecurity, Entra ID, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Intune, Microsoft Purview
Small businesses are not small targets. Threat actors know that organisations with fewer than 50 staff rarely have a dedicated security team. They know Microsoft 365 is the backbone of most Australian SMBs — email, files, Teams, identity. And they know most of those...

by CPI Staff | Apr 18, 2026 | AI Governance & Risk Management, Blog, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Purview
Microsoft’s Deep Research in Copilot for Microsoft 365 has already reshaped how knowledge workers produce long-form analysis. Teams that used to spend days pulling together market scans, risk reviews, and competitive briefings now have a drafting partner that...

by CPI Staff | Jul 29, 2024 | Blog, Exchange Online, Microsoft 365, Microsoft Purview
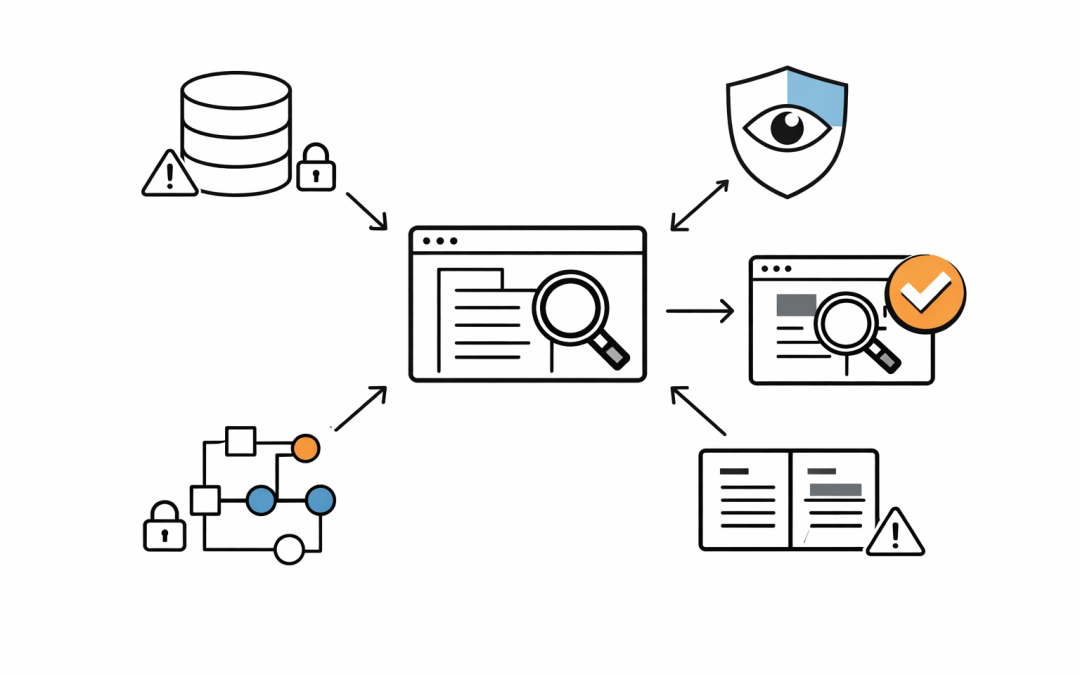
In this Exchange Online and Microsoft Purview article, we will show how to Recover Deleted or Lost Exchange Online Emails to PST. As a consulting company, we help many organisations comply with regulatory requirements like data retention documents, chat history, and...