Most organisations assume that once their devices are enrolled in Microsoft Intune, those devices are secure. That assumption is wrong — and it’s costing them.
There is a default configuration in Intune that silently marks every device without a compliance policy as compliant. No policy assigned? Compliant by default. That’s not a hardened baseline. That’s an open door.
The Gap That Most Teams Miss
When organisations deploy Intune, the focus is on enrolment. Get the devices managed. Push apps. Configure Wi-Fi and email profiles. Compliance policies come later — or sometimes, not at all.
The problem is that Intune’s default tenant-wide setting treats unassigned devices as compliant. Unless an administrator explicitly changes this to “Not compliant”, every device without a policy attached is considered safe.
That includes new devices waiting for policy assignment. BYOD devices that slipped through. Devices that were somehow excluded from a group assignment. All of them look clean to Conditional Access — and Conditional Access will happily let them through to Microsoft 365, SharePoint, and email.
Why Conditional Access Doesn’t Save You Here
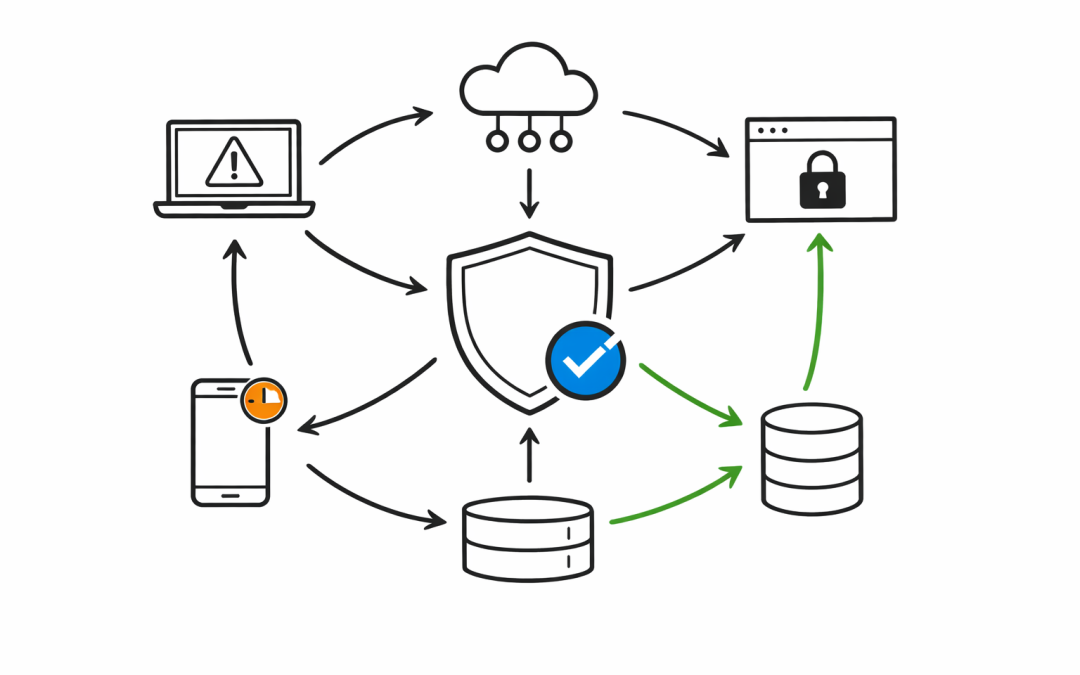
Many IT leaders believe Conditional Access is the safety net. It is — but only if it has accurate compliance signals to work with.
Conditional Access evaluates a device’s compliance status as reported by Intune. If Intune says “compliant,” Conditional Access grants access. If the compliance policy was never assigned in the first place, Intune still says “compliant” by default.
The security control is in place. The data feeding it is incorrect.
This is the gap. It’s not a bug. It’s a misconfiguration — one that ships out of the box.
The Second Gap: Compliance Staleness
Even when compliance policies are assigned correctly, there is a second risk that teams overlook.
Intune has a compliance status validity period — the window during which a device must report in to be considered current. The default is 30 days. A device that hasn’t checked in for 31 days can still be considered compliant in many configurations.
A laptop that was last seen online a month ago could belong to a former employee. It could be outside corporate control. It could be compromised. But if it checks in once every 30 days, Intune has no reason to flag it.
For organisations with mobile workers, remote staff, or a mix of corporate and personal devices, this matters.
What the Australian Context Adds
The Essential 8 framework from the Australian Signals Directorate includes application control, patching, and restricting administrative privileges — all of which depend on knowing that endpoints are in a managed, verified state.
If compliance policies aren’t correctly assigned and enforced, organisations cannot confidently claim Essential 8 compliance, even if they have the right tools deployed. Intune is the enforcement mechanism. A policy gap breaks the chain.
For organisations subject to Australian privacy legislation or sector-specific regulatory requirements, the exposure is not just operational. It’s a compliance risk that auditors will find if IT teams don’t address it first.
What Should Be Done
Closing the Intune policy gap is not complex. It requires deliberate configuration decisions that many deployments skip:
Change the default compliance setting. In Intune, under Endpoint Security > Device Compliance > Compliance Policy Settings, change the setting “Mark devices with no compliance policy assigned as” from Compliant to Not compliant. This one change closes the default-open door.
Audit policy assignments. Review which devices and groups have compliance policies assigned. Identify gaps — particularly for new device types, BYOD, and guest devices. Assign policies to all device groups, not just the obvious ones.
Reduce the validity period. For organisations with higher security requirements, reduce the compliance validity period from 30 days to 7 or 14 days. This ensures devices that go dark are flagged sooner.
Test Conditional Access enforcement. Validate that Conditional Access is actually blocking noncompliant devices, not just checking the setting. Use the Intune compliance dashboard and Entra sign-in logs together to confirm the chain is working end to end.
Review Entra ID device registration. Devices enrolled in Intune register in Microsoft Entra ID. Stale or orphaned device objects can carry old compliance states. Periodic clean-up of inactive device records reduces risk.
The Broader Issue With “Deploy and Forget”
The Intune policy gap is a symptom of a wider pattern. Organisations invest in the right tools, deploy them quickly, and then move on to the next project. The configuration baseline that made sense at launch drifts as the environment grows, changes, and evolves.
Our team sees this regularly with Australian mid-market organisations. Intune is deployed. The basics work. But the compliance and security posture underneath hasn’t been validated against a current threat baseline.
Endpoint management is not a set-and-forget function. It requires periodic review, particularly as device estates grow and workforce patterns change.
Getting It Right From Here
If your organisation has deployed Intune but hasn’t reviewed compliance policy coverage and the default tenant settings, now is the right time.
Our team works with Australian businesses to assess and remediate Intune configurations, align endpoint management to Essential 8 requirements, and ensure that Conditional Access is actually enforcing what it should be.
If you’d like to understand where the gaps are in your current deployment, we’d welcome the conversation.