by CPI Staff | May 14, 2026 | Blog, Cybersecurity, Microsoft 365
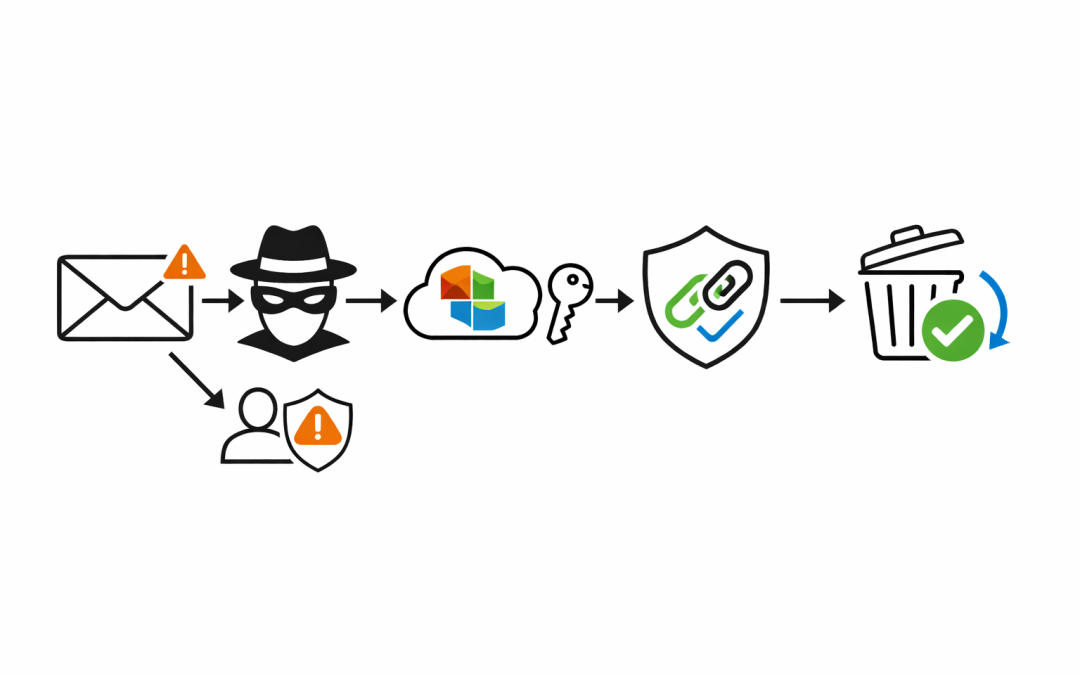
Most phishing discussions still focus on user awareness. That matters, but it is not enough. The real issue for most Australian businesses is that phishing is no longer just a bad email with poor spelling. It is impersonation, credential theft, malicious links that...
by CPI Staff | May 13, 2026 | Blog
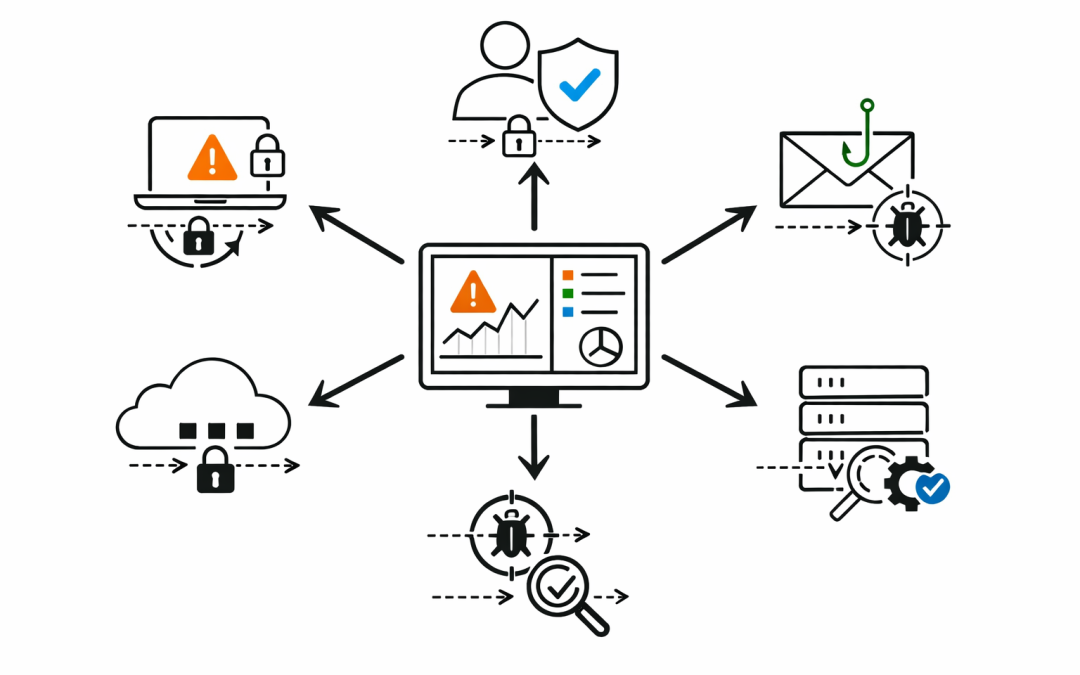
Many small and mid-sized companies assume proper endpoint security means buying a larger, more expensive platform. That often leads to one of two outcomes. They either overspend on capability they will not operate well, or they under-configure the Microsoft security...

by CPI Staff | May 13, 2026 | Blog, Cyber Security Strategy & Governance, Cybersecurity, Endpoint Security, Microsoft 365 Security, Microsoft defender XDR
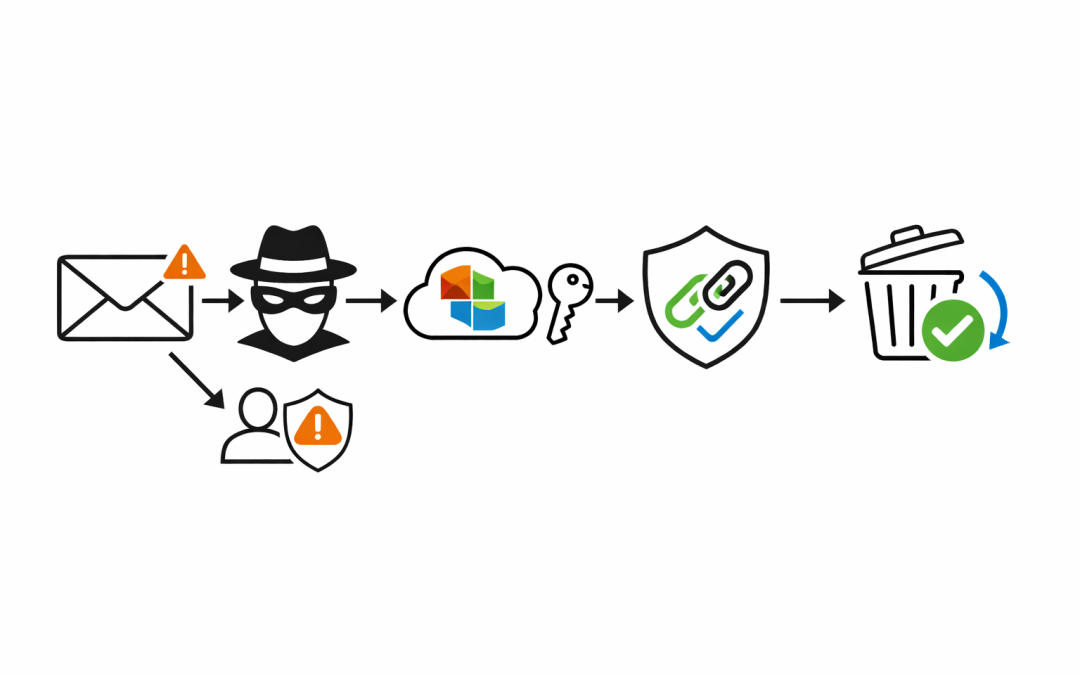
Most breaches do not begin with a sudden, dramatic attack. They begin with a series of signals that were already visible — sitting in a security platform, waiting for someone to act on them. For Australian businesses running Microsoft 365, those signals are already...

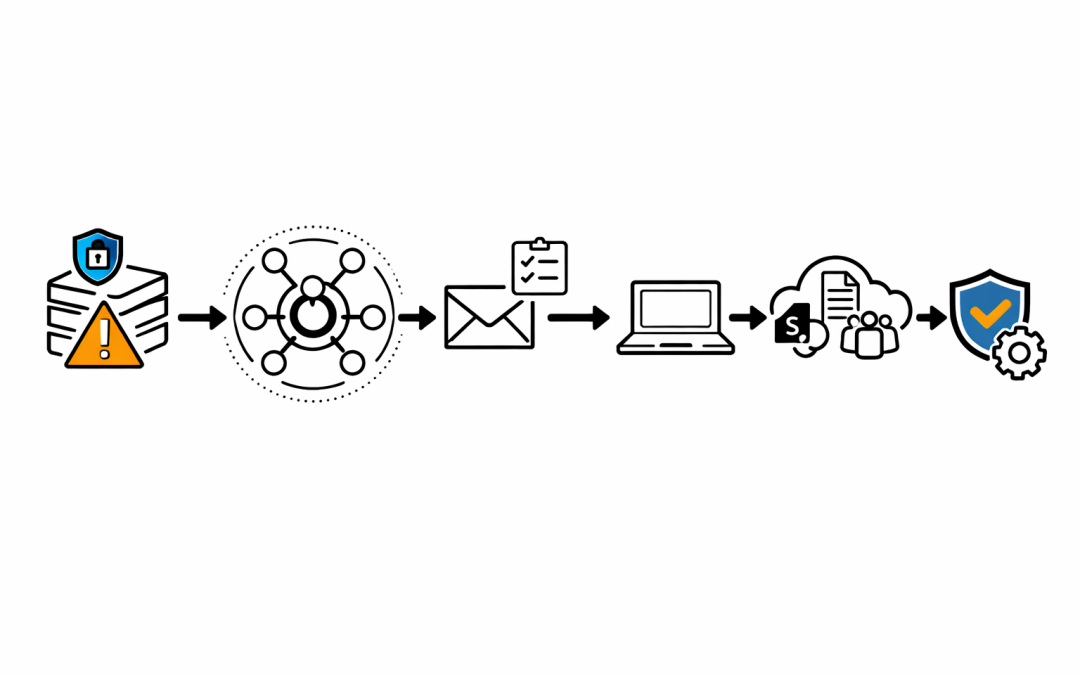
by CPI Staff | May 9, 2026 | Blog, Cybersecurity, Essential 8, Microsoft 365 Security, Microsoft defender XDR
Most security incidents do not begin with a total lack of telemetry. They begin with a signal that was already there, sitting in a queue, waiting for someone to decide whether it mattered. That is the uncomfortable reality for many Microsoft 365 environments....