by CPI Staff | Mar 2, 2026 | AI, Blog, OpenAI
In this blog post OpenAI’s $110B Raise and the New Vendor Lock In Reality for 2026 we will walk through what this funding news really changes for your 2026 budget decisions, and how to get the upside of AI without waking up locked into one vendor, one cloud, and one...

by CPI Staff | Mar 1, 2026 | Blog
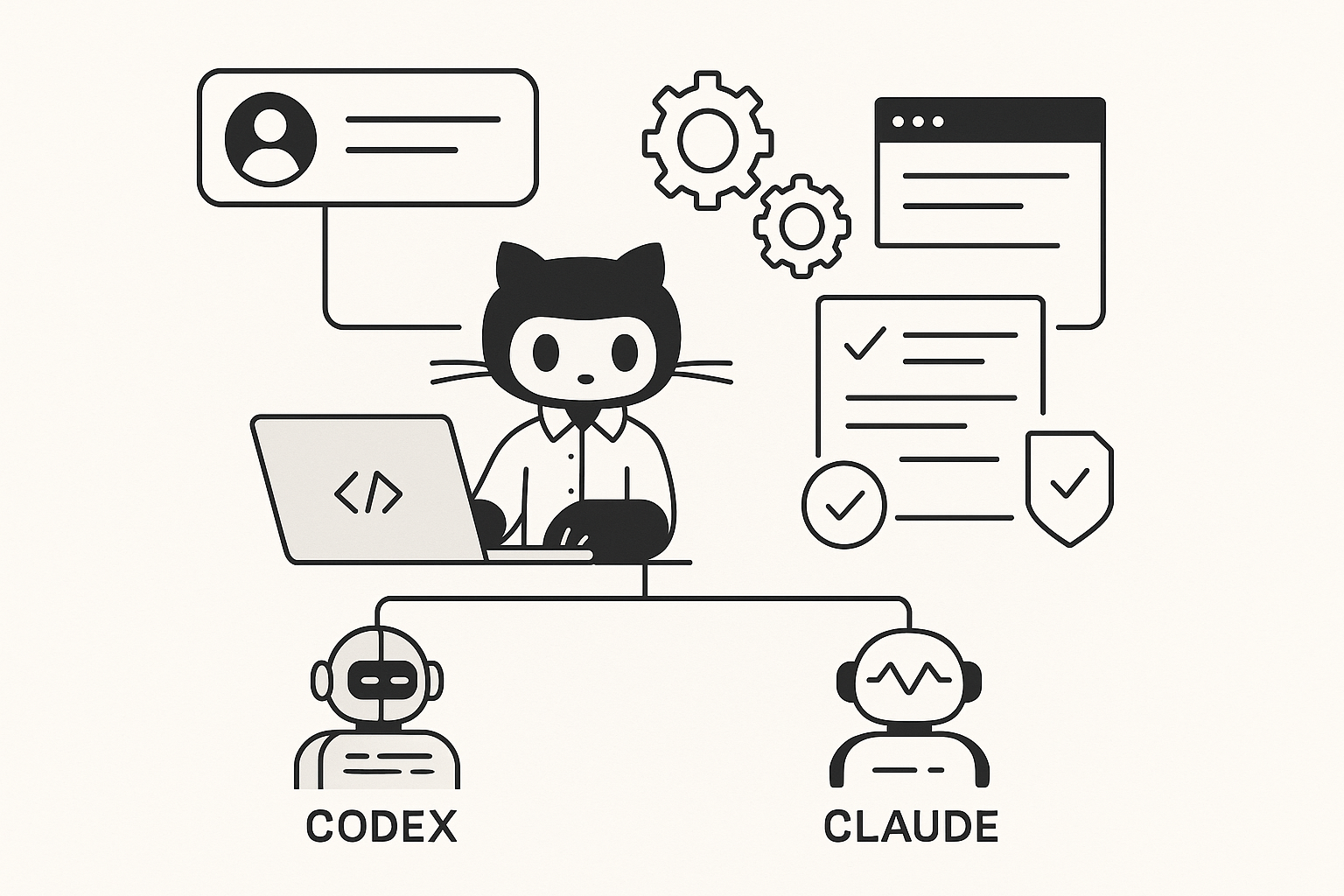
In this blog post Copilot, Codex, Claude Code and GitHub Agents Cut PR Cycle Time 30% we will walk through a practical way to shorten your pull request (PR) cycle time without asking your developers to “work harder” or your tech leaders to accept more risk. If your...

by CPI Staff | Mar 1, 2026 | Blog
In this blog post GitHub Agents with Codex and Claude Cut PR Rework and Security Bugs we will walk through what “GitHub Agents” are, how Codex and Claude Code fit into pull requests (PRs), and the practical ways they reduce rework and security bugs without slowing...

by CPI Staff | Mar 1, 2026 | AI, Blog
In this blog post AI Export Controls Are a Board-Level Risk for Australian Firms we will explain why AI export controls have moved from “someone else’s problem” to a real board-level risk, and what Australian IT and engineering leaders can do about it. If you’re...

by CPI Staff | Mar 1, 2026 | Blog
In this blog post GitHub Agents Make Copilot a Real Dev Team Asset with Codex and Claude we will unpack what GitHub Agents are, why they matter, and how to use them safely so your team ships faster without creating new security or quality risks. If you’ve tried...

by CPI Staff | Mar 1, 2026 | AI, Blog
In this blog post Your Competitor Just Hired an AI Employee And It Works 24/7 we will explain what an “AI employee” really is, why it’s suddenly working in real businesses, and how to build one safely on Microsoft and modern AI platforms. If you’ve had that...