Too many organisations still treat the Essential Eight as a maturity exercise they will get to later. That position is getting harder to defend.
In March 2026, the Australian Cyber Security Centre published a joint advisory on INC Ransom and its affiliate network, warning that the group is actively targeting organisations across Australia, New Zealand and the Pacific. For Australian businesses, this is not another generic ransomware bulletin. It is a clear reminder that the gap between basic controls and operationally mature controls is where real damage now happens.
For many mid-market organisations, Essential Eight Maturity Level Two is the point where cyber hygiene starts to become meaningful resistance rather than box-ticking.
Why This Advisory Matters
The ACSC advisory describes INC Ransom as a ransomware-as-a-service operation using affiliates to compromise organisations, steal data, encrypt systems and then pressure victims through double extortion. In other words, the attackers do not just want to disrupt systems. They want leverage.
The Australian data in the advisory is specific enough to matter. Between 1 July 2024 and 31 December 2025, the ACSC responded to 11 reported INC Ransom-related incidents in Australia, with Professional Services and Health Care affected most heavily. Since January 2025, the ACSC has observed affiliates targeting Australian health care entities through compromised accounts, creating administrator-level accounts, moving laterally and exfiltrating personally identifiable and medical information.
That attack pattern should feel familiar to every CIO and IT leader. It is not exotic tradecraft. It is a disciplined combination of credential abuse, weak remote access posture, privilege escalation, lateral movement and poor containment.
The Real Lesson Is Not Just “Patch Faster”
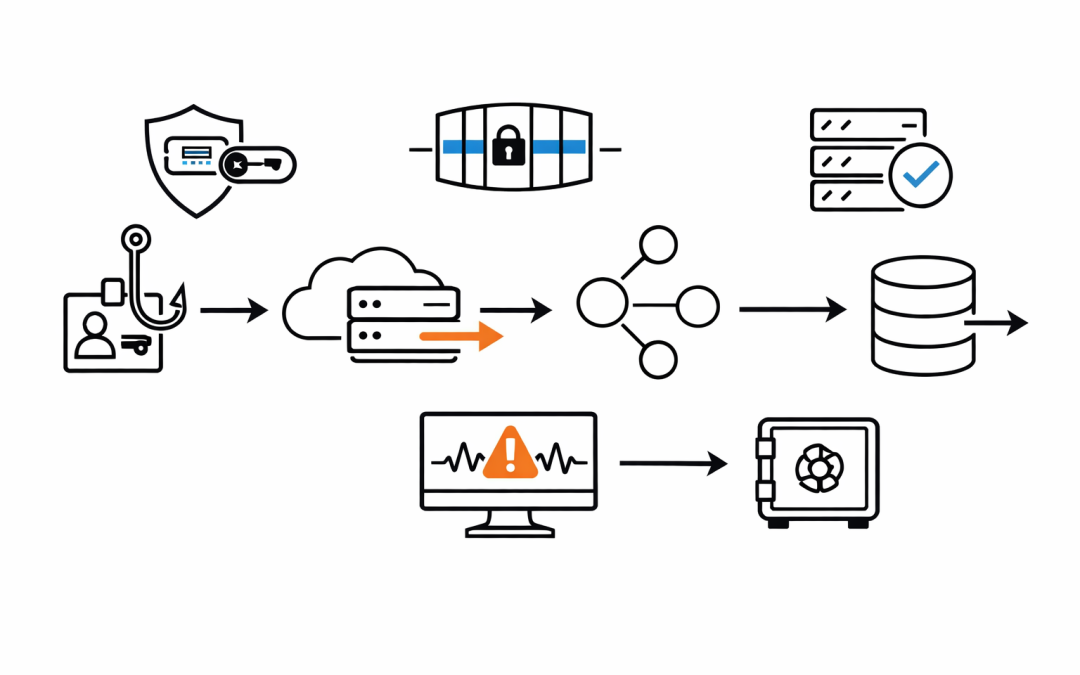
The ACSC notes that INC Ransom affiliates commonly gain initial access through spear-phishing, compromised credentials and exploitation of known vulnerabilities in unpatched internet-facing devices. They also use legitimate tools such as 7-Zip, WinRAR and rclone to compress and exfiltrate data.
That matters because many organisations still think ransomware defence starts and ends with endpoint protection and backups. It does not. If attackers can sign in with valid accounts, bypass weak access controls, escalate privileges and use normal administration pathways, then a lot of downstream security tooling becomes reactive instead of preventative.
This is exactly why the ACSC’s Essential Eight maturity model is useful. It does not ask whether an organisation has a control on paper. It asks whether the control is implemented at a level that matches how today’s attackers actually operate.
Why Maturity Level Two Changes The Discussion
The ACSC describes Maturity Level Two as being focused on malicious actors who are willing to invest more time in a target, improve the effectiveness of their tools, actively target credentials through phishing and use technical and social engineering techniques to circumvent weak multi-factor authentication.
That description maps closely to the INC Ransom campaign. This is the practical reason ML2 should now be the default target for many Australian organisations. It is the maturity level designed for adversaries who are no longer purely opportunistic but are still common enough to be a mainstream business risk.
Maturity Level One is still valuable. But if the threat includes targeted phishing, credential abuse, weak MFA bypass, privilege misuse and ransomware operators looking for the fastest path to impact, ML1 often leaves too much room for the attack to succeed.
The ML2 Controls That Matter Most Against INC Ransom
Phishing-Resistant MFA
This is one of the biggest shifts from “we have MFA” to “our MFA posture can withstand modern attacks”. At ML2, phishing-resistant MFA is required for users of online services and systems, and customers must be offered a phishing-resistant option for online customer services.
That matters because the ACSC advisory explicitly highlights compromised accounts and the need to prioritise phishing-resistant MFA for remote access services, online services and privileged accounts. Push notifications and weak second factors are no longer enough in environments where attackers are deliberately targeting credentials.
Privileged Access Controls
The advisory observed INC Ransom affiliates creating new admin accounts and using privileged access to move laterally. ML2 responds directly to that problem.
It requires dedicated privileged accounts, time-bound revalidation of privileged access, inactivity-based disabling of privileged access, separation of privileged and unprivileged environments, and stronger logging around privileged events. Those are not compliance details. They are the controls that stop a single compromised identity from becoming an environment-wide incident.
Faster, Broader Vulnerability Management
The ACSC advisory points to unpatched internet-facing devices as a common initial access path. ML2 reinforces that reality by requiring regular vulnerability scanning, patching of critical or exploited online services within 48 hours, and structured patching across operating systems and a broader application estate.
The practical difference is important. Many organisations patch their headline systems eventually. ML2 pushes them toward a repeatable program that finds exposed assets, prioritises exploitable weaknesses and closes the window attackers rely on.
Application Control And Hardening
INC Ransom affiliates rely on tooling, scripting and legitimate utilities to progress an intrusion. ML2 strengthens resistance by extending application control to internet-facing servers, applying Microsoft’s recommended blocklist, hardening browsers and Office, blocking risky child-process behaviour and improving PowerShell and command-line logging.
Those measures do not eliminate every intrusion path, but they materially reduce an attacker’s ability to execute, persist and expand once access is gained.
Logging, Detection And Response Discipline
One of the less-discussed strengths of ML2 is that it is not just a prevention model. It also expects central logging, protection of logs from tampering, timely analysis of cyber security events and enactment of the incident response plan when an incident is identified.
That aligns with the ACSC advisory’s detection guidance, which calls for centralised logs, monitoring of unauthorised remote access, and hunting for indicators of compromise linked to INC Ransom tactics. If an organisation cannot see privilege changes, remote access misuse, brute-force attempts or unusual internal scanning quickly, it will discover ransomware far too late.
Backup Resilience
Backups still matter, but only if attackers cannot reach them. ML2 strengthens backup integrity by preventing modification and deletion by unprivileged users and restricting backup access for privileged accounts other than backup administrators.
That is a material step up for organisations that still rely on backup architectures that are too exposed to the same identities attackers compromise first.
What Business Leaders Should Take From This
The key takeaway is not that every organisation must instantly jump to Maturity Level Three. It is that many Australian organisations are now operating against threat patterns that ML2 was specifically designed to address.
If your environment still depends on weak MFA, broad admin access, patch cycles that lag behind public exploitation, limited server-side application control and incomplete security logging, then the issue is no longer theoretical maturity. It is operational exposure.
Boards and executive teams should treat ML2 as a business resilience baseline for internet-connected enterprise environments, especially those handling sensitive customer, health, legal or financial information. The cost of remaining below that level is increasingly visible in real incidents.
Where To Start
For most mid-market organisations, the right next step is not to launch a massive transformation program. It is to identify which ML2 gaps would matter most during a real ransomware intrusion.
That usually means starting with phishing-resistant MFA, privileged access separation, patching of internet-facing assets, backup protection, and central logging that can actually support rapid investigation.
The organisations that respond best to campaigns like INC Ransom are usually not the ones with the biggest security stack. They are the ones that have made their baseline controls difficult to bypass.
We help Australian organisations assess where their Essential Eight posture will hold up under current attack patterns and where it will not. If the latest ACSC advisory has raised questions about your path to ML2, our team can help you prioritise the controls that reduce risk fastest.