by CPI Staff | Apr 21, 2026 | AI, Blog, Cybersecurity
For many organisations, AI risk has been treated as a future governance issue. The Australian Cyber Security Centre has just made that position harder to defend. In its 9 April 2026 guidance, Frontier models and their impact on cyber security, ACSC draws a direct line...
by CPI Staff | Apr 18, 2026 | AI, AI Agents, AI for Business & AI Strategy, AI Governance & Risk Management, AI Vendor Selection & Implementation, Anthropic, Blog, Claude
Anthropic’s release of Claude Opus 4.7 isn’t just another model refresh. For organisations running agentic workloads — the kind that chain tool calls, browse systems, write and execute code, and make decisions across long-running tasks — this release moves...

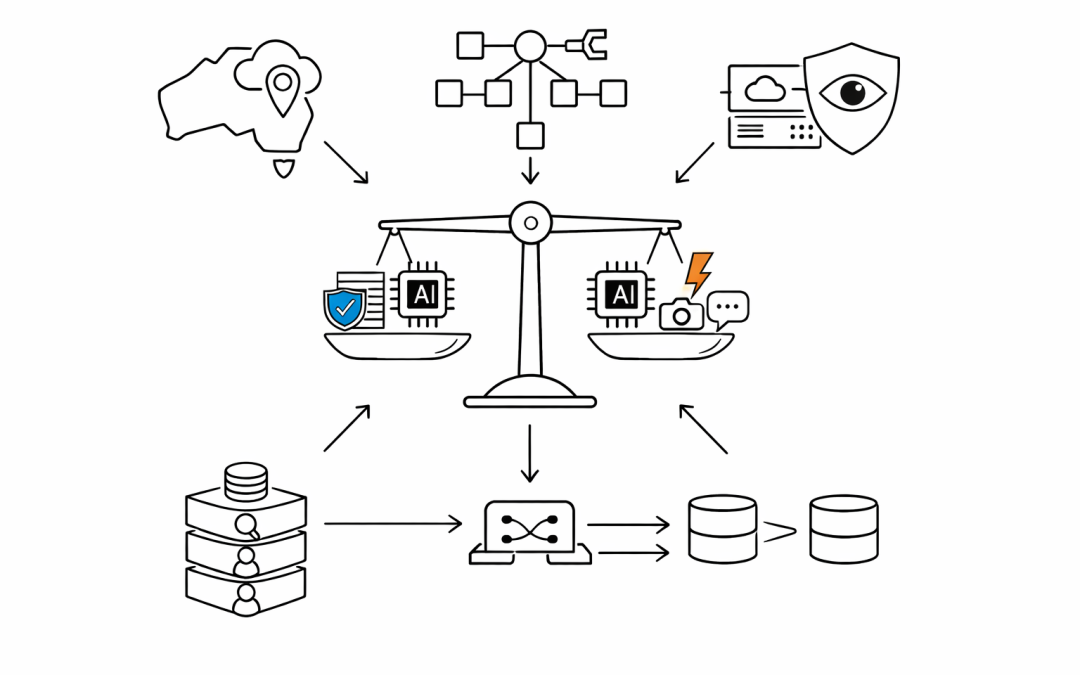
by CPI Staff | Apr 17, 2026 | AI, AI for Business & AI Strategy, AI Vendor Selection & Implementation, Anthropic, Blog, Claude, LLM, OpenAI
Every few months, the frontier model leaderboard shifts again. Anthropic’s Claude Opus 4.7 and OpenAI’s GPT-5.4 are the latest pair of heavyweights competing for enterprise budgets — and the decision is no longer just about benchmark scores. For Australian...

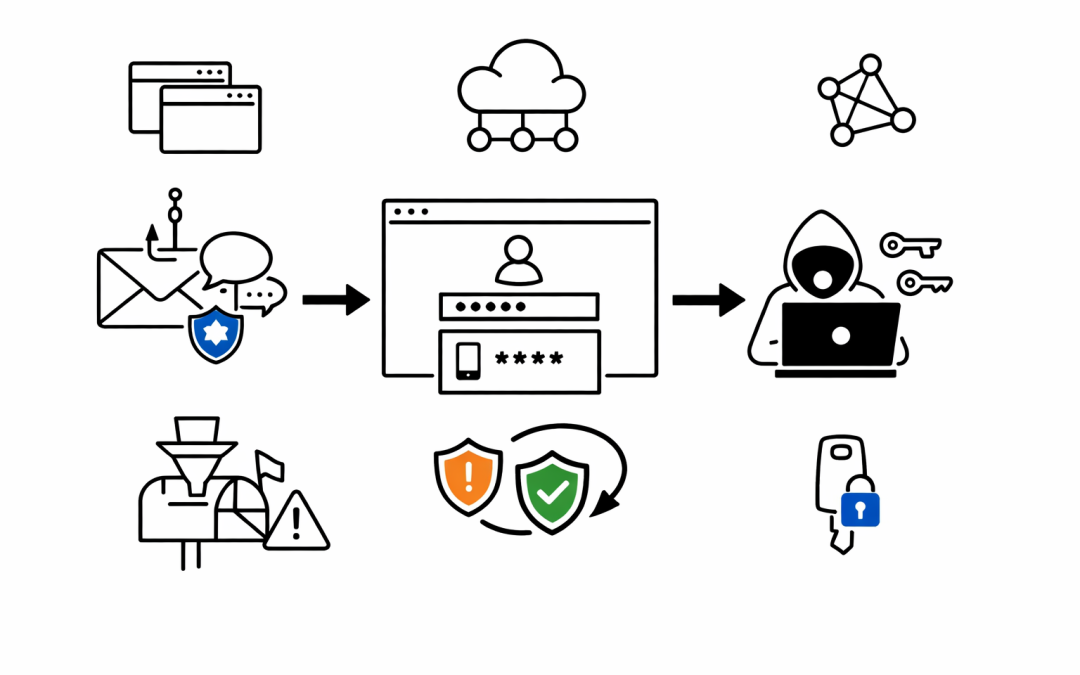
by CPI Staff | Apr 9, 2026 | AI, Blog, Cybersecurity, Entra ID, Microsoft 365 Security
Multi-factor authentication has been the security baseline for years. Most Australian organisations treat it as the final checkpoint — if MFA is in place, accounts are protected. That assumption just got a serious challenge. Microsoft Defender Security Research has...

by CPI Staff | Apr 4, 2026 | AI, AI Agents, Blog
Zero Trust is well understood for users. Verify identity, check device health, enforce least privilege, assume breach. Most mature IT organisations have some version of this in place. AI agents break that model. Not because Zero Trust principles are wrong — but...

by CPI Staff | Apr 3, 2026 | AI, Blog, Google
Google’s Threat Intelligence Group just published one of the most detailed reports to date on how adversaries are using AI to accelerate attacks. For Australian CISOs, five findings demand immediate attention. The GTIG AI Threat Tracker, published in early 2026...