by CPI Staff | Feb 2, 2026 | Blog, GitHub
In this blog post Use GitHub Copilot Agent Skills Without Blowing Your Context Window we will explain what Agent Skills are, how they work under the hood, and how to design them so Copilot stays helpful without dragging your entire repo (and your patience) into every...

by CPI Staff | Feb 1, 2026 | Blog, Microsoft Intune
In this blog post Enforce Device Compliance with Microsoft Intune for Safer Access we will walk through how to use Microsoft Intune to define “good device hygiene,” measure it continuously, and then enforce it at sign-in time. The goal is simple: let productive work...

by CPI Staff | Feb 1, 2026 | Blog, LangChain
In this blog post Protect Against LangGrinch CVE-2025-68664 in LangChain Apps we will walk through what the vulnerability is, why it matters, and the practical steps you can take to reduce risk in real-world LangChain deployments. LangChain is popular because it helps...
by CPI Staff | Jan 30, 2026 | Blog, GitHub Copilot CLI
In this blog post Parallel Code Review with GitHub Copilot CLI for Faster PRs we will walk through a practical way to run several AI-assisted review passes at the same time, directly from your terminal. The goal is simple: reduce review bottlenecks, raise code...

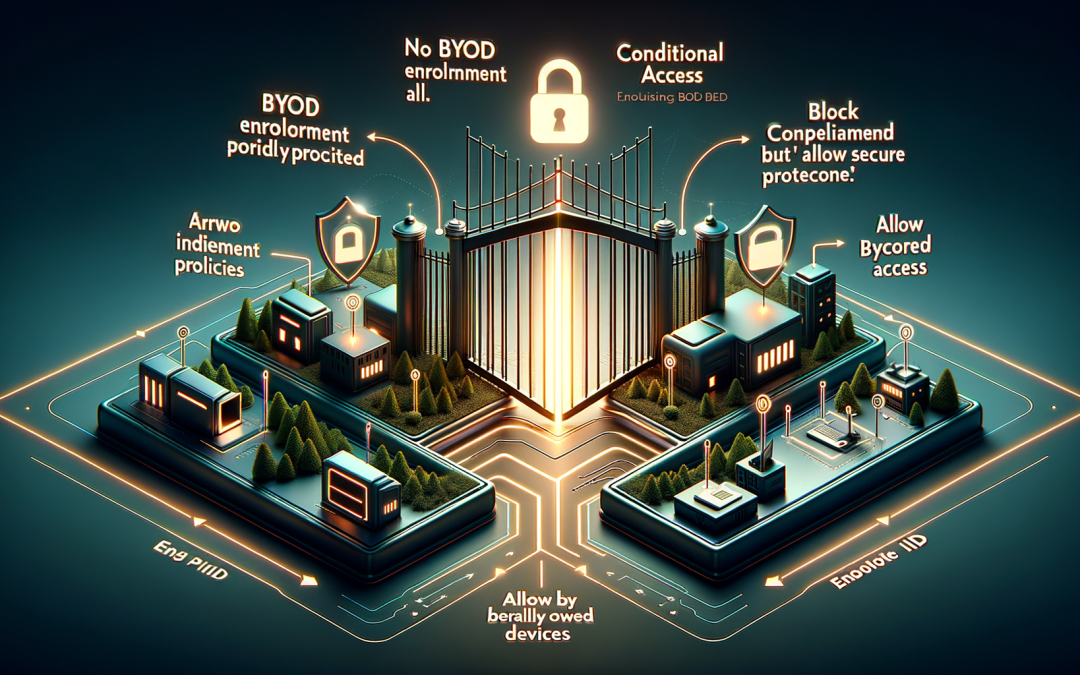
by CPI Staff | Jan 29, 2026 | Blog, Microsoft Intune
In this blog post Block Personally Owned Devices with Microsoft Intune for Better Security we will explain how to stop personally owned devices (BYOD) from enrolling into Intune, why it matters, and how to do it safely without breaking legitimate business workflows....