On April 7, 2026, Anthropic announced Project Glasswing — a cybersecurity initiative that brings together AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks. Their shared mission: use frontier AI to find and fix vulnerabilities in the world’s most critical software before attackers do.
For enterprise security teams already stretched thin, this is worth paying close attention to.
The Catalyst: AI Models That Out-Hack Most Humans
Project Glasswing exists because of something Anthropic observed in Claude Mythos Preview, an unreleased frontier model. This model has reached a level of coding and reasoning capability where it can surpass all but the most skilled humans at finding and exploiting software vulnerabilities.
That is not a theoretical concern. Mythos Preview has already discovered thousands of zero-day vulnerabilities across every major operating system and every major web browser — many of them critical.
Among the findings: a 27-year-old vulnerability in OpenBSD, widely regarded as one of the most security-hardened operating systems in existence. A 16-year-old flaw in FFmpeg that automated testing tools had hit five million times without detecting. And several chained Linux kernel vulnerabilities that allowed full privilege escalation from ordinary user access.
These flaws survived decades of human code review and millions of automated scans.
Why This Matters for Enterprise Security Teams
The implications are stark. If an AI model built by a responsible lab can find vulnerabilities that eluded the world’s best human reviewers for decades, it is only a matter of time before similar capabilities proliferate to threat actors.
As CrowdStrike CTO Elia Zaitsev put it: “The window between a vulnerability being discovered and being exploited by an adversary has collapsed — what once took months now happens in minutes with AI.”
For mid-market Australian organisations running 50 to 500 seats, this changes the risk equation significantly. Most enterprises rely heavily on open-source components, third-party libraries, and the same operating systems and browsers that Mythos Preview found riddled with flaws. The attack surface is shared, and the defensive tools available to most security teams have not kept pace with what frontier AI can now do.
What Project Glasswing Actually Delivers
Anthropic is committing up to $100 million in usage credits for Claude Mythos Preview across the initiative, plus $4 million in direct donations to open-source security organisations — including $2.5 million to Alpha-Omega and OpenSSF through the Linux Foundation, and $1.5 million to the Apache Software Foundation.
The 12 launch partners are using Mythos Preview for defensive security work across their foundational systems. Over 40 additional organisations that build or maintain critical software infrastructure have also been granted access.
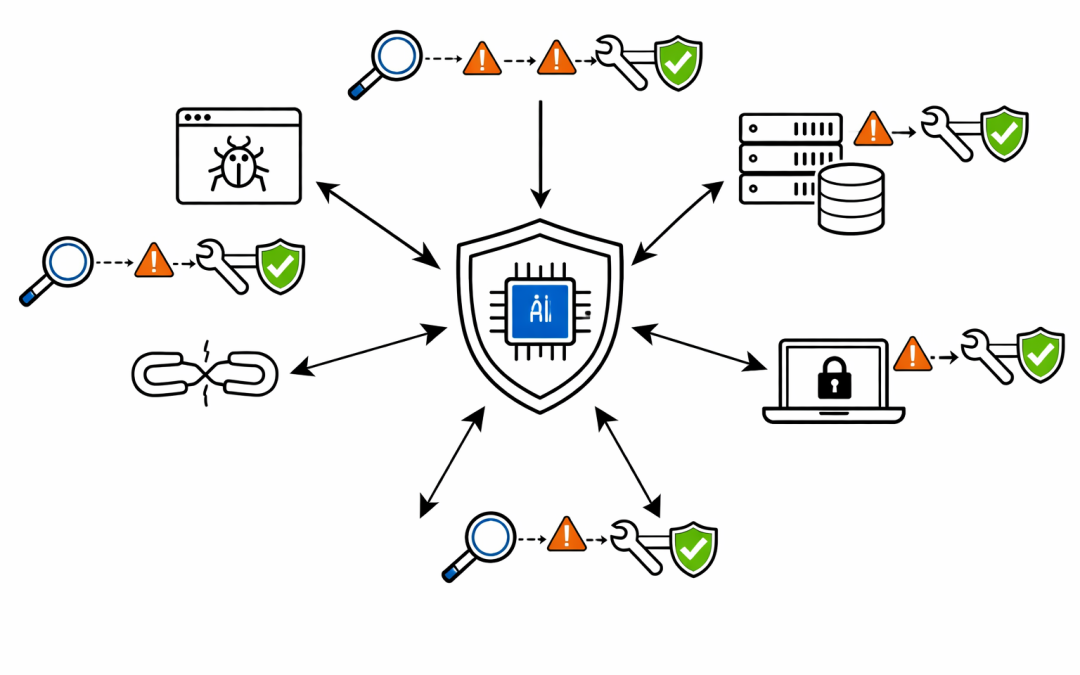
The practical focus areas include local vulnerability detection, black-box testing of binaries, endpoint hardening, and penetration testing of systems — all powered by AI that can reason about code in ways no scanner could previously match.
Within 90 days, Anthropic has committed to reporting publicly on what the initiative has learned, including vulnerabilities fixed and recommendations for how security practices should evolve.
The Open-Source Angle Australian Organisations Cannot Ignore
Linux Foundation CEO Jim Zemlin highlighted what many enterprise security professionals already know: open-source maintainers — whose software underpins the majority of modern enterprise systems — have historically lacked the resources for comprehensive security testing.
Project Glasswing aims to change that by giving maintainers of critical open-source codebases access to frontier AI models that can proactively identify and fix vulnerabilities at scale.
For organisations running workloads on Linux, relying on open-source libraries across their application stack, or consuming software built on these foundations, this is directly relevant. When upstream dependencies get more secure, the entire ecosystem benefits.
What This Signals for Security Strategy
Project Glasswing represents a shift in how the industry thinks about AI and cybersecurity. The key takeaways for enterprise security leaders:
Vulnerability discovery is being democratised. What once required elite-level security researchers can now be performed by AI models. This is true for defenders and attackers alike. Security strategies built on the assumption that complex vulnerabilities are hard to find need urgent revision.
Patching velocity matters more than ever. When AI can find and exploit flaws in minutes, slow patching cycles become existential risks. Organisations that cannot deploy patches rapidly across their estate face significantly elevated exposure.
AI-augmented security is becoming table stakes. The major security vendors — CrowdStrike, Palo Alto Networks, Microsoft, Google — are all participating in Glasswing. Their products will increasingly incorporate these capabilities. Organisations that do not adopt AI-enhanced security tooling risk falling behind the threat curve.
Supply chain security needs a rethink. With AI models capable of finding vulnerabilities that survived decades of human review, every dependency in the software supply chain becomes a potential attack vector. Third-party risk assessment frameworks need to account for this new reality.
The Australian Context
For Australian organisations operating under the Essential Eight framework, Project Glasswing reinforces the urgency of several controls — particularly patching applications, patching operating systems, and restricting administrative privileges.
The ACSC has consistently warned about the increasing sophistication of cyber threats targeting Australian businesses. AI-powered vulnerability discovery accelerates this trend dramatically. Organisations that have treated Essential Eight maturity as a compliance checkbox rather than a genuine security posture improvement need to reconsider their approach.
What Organisations Should Do Now
The good news is that Project Glasswing puts these capabilities in the hands of defenders first. But waiting for the benefits to trickle down is not a strategy.
Enterprise security teams should be reviewing their current vulnerability management processes, patching cadences, and dependency inventories. They should be evaluating how AI-enhanced security tools can augment their existing capabilities. And they should be having honest conversations about whether their current security posture can withstand the threat landscape that frontier AI creates.
The organisations that act now — before AI-powered attacks become commonplace — will be the ones best positioned to weather what comes next.
Our team at CPI Consulting helps Australian organisations strengthen their cybersecurity posture with practical, hands-on guidance across Microsoft Defender, Wiz, and the Essential Eight. If your organisation needs help navigating the evolving threat landscape, reach out for a conversation.